通用密钥库密码算法规格
规格实现范围说明
本文档将说明密钥管理服务规格全景,面向OpenHarmony的厂商适配密钥管理服务规格分为必选规格和可选规格。必选规格为所有厂商均支持的算法规格。而对于可选规格,厂商将基于实际情况决定是否实现,如需使用,请查阅具体厂商提供的说明,确保规格支持再使用。 建议开发者使用必选规格开发应用,可保证全平台兼容。
支持的算法类型及参数组合
导入\生成密钥规格
| 算法 | API级别 | 支持的密钥长度 | 是否必选规格 |
|---|---|---|---|
| AES | 8+ | 128、192、256 | 是 |
| RSA | 8+ | 512、768、1024 | 否 |
| RSA | 8+ | 2048、3072、4096 | 是 |
| HMAC | 8+ | 8-1024(含),必须是8的倍数 | 是 |
| ECC | 8+ | 224 | 否 |
| ECC | 8+ | 256、384、521 | 是 |
| ED25519 | 8+ | 256 | 是 |
| X25519 | 8+ | 256 | 是 |
| DSA | 8+ | 512-1024(含),8的倍数 | 否 |
| DH | 8+ | 2048 | 是 |
| DH | 8+ | 3072、4096 | 否 |
| SM2 | 9+ | 256 | 是 |
| SM4 | 9+ | 128 | 是 |
加密&解密流程算法与分组、填充模式的组合规格
| 算法/分组模式/填充模式 | API级别 | 备注 | 是否必选规格 |
|---|---|---|---|
| AES/ECB/NoPadding AES/ECB/PKCS7 |
8+ | 否 | |
| AES/CBC/NoPadding AES/CBC/PKCS7 AES/CTR/NoPadding |
8+ | IV参数必选 | 是 |
| AES/GCM/NoPadding | 8+ | Nonce、AAD、AEAD参数必选 | 是 |
| RSA/ECB/NoPadding RSA/ECB/PKCS1_V1_5 RSA/ECB/OAEP |
8+ | OAEP填充模式支持的摘要算法:SHA256/SHA384/SHA512 | 是 |
| SM4/ECB/NoPadding SM4/ECB/PKCS7 SM4/CBC/PKCS7 |
9+ | CBC模式下 IV 参数必选 | 否 |
| SM4/CTR/NoPadding SM4/CBC/NoPadding |
9+ | IV 参数必选 | 是 |
签名&验签流程算法与摘要算法、填充模式的组合规格
| 算法/摘要算法/填充模式 | API级别 | 备注 | 是否必选规格 |
|---|---|---|---|
| RSA/MD5/PKCS1_V1_5 RSA/SHA1/PKCS1_V1_5 RSA/SHA224/PKCS1_V1_5 RSA/SHA224/PSS |
8+ | 否 | |
| RSA/SHA256/PKCS1_V1_5 RSA/SHA384/PKCS1_V1_5 RSA/SHA512/PKCS1_V1_5 RSA/SHA256/PSS RSA/SHA384/PSS RSA/SHA512/PSS |
8+ | 是 | |
| RSA/NoDigest/PKCS1_V1_5 | 9+ | NoDigest 需要指定TAG HuksKeyDigest.HUKS_DIGEST_NONE | 否 |
| DSA/SHA1 DSA/SHA224 DSA/SHA256 DSA/SHA384 DSA/SHA512 |
8+ | 否 | |
| DSA/NoDigest | 9+ | NoDigest 需要指定TAG HuksKeyDigest.HUKS_DIGEST_NONE | 否 |
| ECC/SHA1 ECC/SHA224 |
8+ | 否 | |
| ECC/SHA256 ECC/SHA384 ECC/SHA512 |
8+ | 是 | |
| ECC/NoDigest | 9+ | NoDigest 需要指定TAG HuksKeyDigest.HUKS_DIGEST_NONE | 否 |
| ED25519/NoDigest | 8+ | NoDigest 需要指定TAG HuksKeyDigest.HUKS_DIGEST_NONE | 是 |
| SM2/SM3 | 9+ | 是 |
密钥协商算法
| 算法 | API级别 | 备注 | 是否必选规格 |
|---|---|---|---|
| ECDH | 8+ | 协商密钥类型为ECC类型密钥 | 是 |
| DH | 8+ | 是 | |
| X25519 | 8+ | 是 |
HMAC 密钥长度与摘要组合规格
| 摘要 | 密钥长度 | API级别 | 是否必选规格 |
|---|---|---|---|
| SHA256 | 192-1024(8的倍数) | 8+ | 是 |
| SHA384 | 256-1024(8的倍数) | 8+ | 是 |
| SHA512 | 256-1024(8的倍数) | 8+ | 是 |
派生算法/摘要组合规格
| 算法/摘要 | 派生密钥的算法/长度 | 派生结果密钥可用算法/长度 | 备注 | API级别 | 是否必选规格 |
|---|---|---|---|---|---|
| HKDF/SHA256 | AES/192-256 | AES/128/192/256 HMAC/8-1024 SM4/128 |
派生密钥是业务基于三段式得到密钥会话结果,业务可决定派生密钥是否由HUKS管理(即密钥不出TEE)亦或是业务独立管理 | 8+ | 是 |
| HKDF/SHA384 | AES/256 | AES/128/192/256 HMAC/8-1024 SM4/128 |
派生密钥是业务基于三段式得到密钥会话结果,业务可决定派生密钥是否由HUKS管理(即密钥不出TEE)亦或是业务独立管理 | 8+ | 是 |
| HKDF/SHA512 | AES/256 | AES/128/192/256 HMAC/8-1024 SM4/128 |
派生密钥是业务基于三段式得到密钥会话结果,业务可决定派生密钥是否由HUKS管理(即密钥不出TEE)亦或是业务独立管理 | 8+ | 是 |
| PBKDF2/SHA256 | AES/192-256 | AES/128/192/256 HMAC/8-1024 SM4/128 |
派生密钥是业务基于三段式得到密钥会话结果,业务可决定派生密钥是否由HUKS管理(即密钥不出TEE)亦或是业务独立管理 | 8+ | 是 |
| PBKDF2/SHA384 | AES/256 | AES/128/192/256 HMAC/8-1024 SM4/128 |
派生密钥是业务基于三段式得到密钥会话结果,业务可决定派生密钥是否由HUKS管理(即密钥不出TEE)亦或是业务独立管理 | 8+ | 是 |
| PBKDF2/SHA512 | AES/256 | AES/128/192/256 HMAC/8-1024 SM4/128 |
派生密钥是业务基于三段式得到密钥会话结果,业务可决定派生密钥是否由HUKS管理(即密钥不出TEE)亦或是业务独立管理 | 8+ | 是 |
密钥证明
| 算法 | API级别 | 备注 | 是否必选规格 |
|---|---|---|---|
| RSA | 9+ | 支持Padding为 PSS 与 PKCS1_V1_5的密钥 | 是 |
| ECC | 9+ | 是 | |
| X25519 | 9+ | 是 |
密钥材料格式
针对不同密码算法的密钥对、公钥、私钥,HUKS定义了一套密钥材料格式。
密钥对材料
密钥对材料 = 密钥对材料Header + 密钥对材料原文
以RSA密钥为例,应用需要申请一个Uint8Array,按照RSA密钥对材料内存格式,将各个变量赋值到对应的位置:
图1 RSA密钥材料内存结构
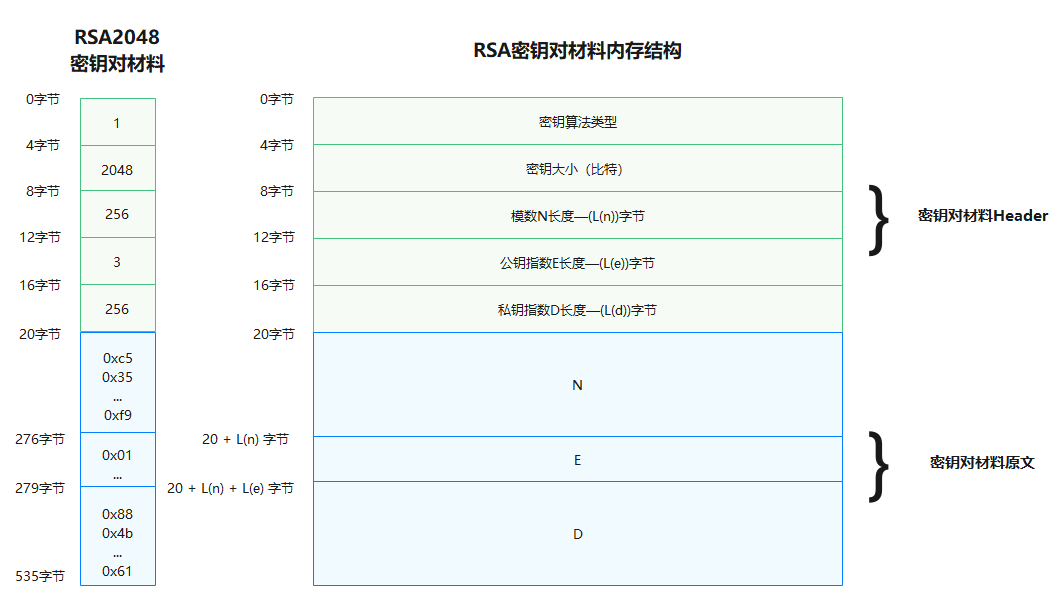
let rsa2048KeyPairMaterial = new Uint8Array([
0x01, 0x00, 0x00, 0x00, // 密钥算法:huks.HuksKeyAlg.HUKS_ALG_RSA = 1
0x00, 0x08, 0x00, 0x00, // 密钥大小(比特):2048
0x00, 0x01, 0x00, 0x00, // 模数n长度(字节):256
0x03, 0x00, 0x00, 0x00, // 公钥指数e长度(字节):3
0x00, 0x01, 0x00, 0x00, // 私钥指数d长度(字节):256
// 模数n
0xc5, 0x35, 0x62, 0x48, 0xc4, 0x92, 0x87, 0x73, 0x0d, 0x42, 0x96, 0xfc, 0x7b, 0x11, 0x05, 0x06,
0x0f, 0x8d, 0x66, 0xc1, 0x0e, 0xad, 0x37, 0x44, 0x92, 0x95, 0x2f, 0x6a, 0x55, 0xba, 0xec, 0x1d,
0x54, 0x62, 0x0a, 0x4b, 0xd3, 0xc7, 0x05, 0xe4, 0x07, 0x40, 0xd9, 0xb7, 0xc2, 0x12, 0xcb, 0x9a,
0x90, 0xad, 0xe3, 0x24, 0xe8, 0x5e, 0xa6, 0xf8, 0xd0, 0x6e, 0xbc, 0xd1, 0x69, 0x7f, 0x6b, 0xe4,
0x2b, 0x4e, 0x1a, 0x65, 0xbb, 0x73, 0x88, 0x6b, 0x7c, 0xaf, 0x7e, 0xd0, 0x47, 0x26, 0xeb, 0xa5,
0xbe, 0xd6, 0xe8, 0xee, 0x9c, 0xa5, 0x66, 0xa5, 0xc9, 0xd3, 0x25, 0x13, 0xc4, 0x0e, 0x6c, 0xab,
0x50, 0xb6, 0x50, 0xc9, 0xce, 0x8f, 0x0a, 0x0b, 0xc6, 0x28, 0x69, 0xe9, 0x83, 0x69, 0xde, 0x42,
0x56, 0x79, 0x7f, 0xde, 0x86, 0x24, 0xca, 0xfc, 0xaa, 0xc0, 0xf3, 0xf3, 0x7f, 0x92, 0x8e, 0x8a,
0x12, 0x52, 0xfe, 0x50, 0xb1, 0x5e, 0x8c, 0x01, 0xce, 0xfc, 0x7e, 0xf2, 0x4f, 0x5f, 0x03, 0xfe,
0xa7, 0xcd, 0xa1, 0xfc, 0x94, 0x52, 0x00, 0x8b, 0x9b, 0x7f, 0x09, 0xab, 0xa8, 0xa4, 0xf5, 0xb4,
0xa5, 0xaa, 0xfc, 0x72, 0xeb, 0x17, 0x40, 0xa9, 0xee, 0xbe, 0x8f, 0xc2, 0xd1, 0x80, 0xc2, 0x0d,
0x44, 0xa9, 0x59, 0x44, 0x59, 0x81, 0x3b, 0x5d, 0x4a, 0xde, 0xfb, 0xae, 0x24, 0xfc, 0xa3, 0xd9,
0xbc, 0x57, 0x55, 0xc2, 0x26, 0xbc, 0x19, 0xa7, 0x9a, 0xc5, 0x59, 0xa3, 0xee, 0x5a, 0xef, 0x41,
0x80, 0x7d, 0xf8, 0x5e, 0xc1, 0x1d, 0x32, 0x38, 0x41, 0x5b, 0xb6, 0x92, 0xb8, 0xb7, 0x03, 0x0d,
0x3e, 0x59, 0x0f, 0x1c, 0xb3, 0xe1, 0x2a, 0x95, 0x1a, 0x3b, 0x50, 0x4f, 0xc4, 0x1d, 0xcf, 0x73,
0x7c, 0x14, 0xca, 0xe3, 0x0b, 0xa7, 0xc7, 0x1a, 0x41, 0x4a, 0xee, 0xbe, 0x1f, 0x43, 0xdd, 0xf9,
// 公钥指数e
0x01, 0x00, 0x01,
// 私钥指数d
0x88, 0x4b, 0x82, 0xe7, 0xe3, 0xe3, 0x99, 0x75, 0x6c, 0x9e, 0xaf, 0x17, 0x44, 0x3e, 0xd9, 0x07,
0xfd, 0x4b, 0xae, 0xce, 0x92, 0xc4, 0x28, 0x44, 0x5e, 0x42, 0x79, 0x08, 0xb6, 0xc3, 0x7f, 0x58,
0x2d, 0xef, 0xac, 0x4a, 0x07, 0xcd, 0xaf, 0x46, 0x8f, 0xb4, 0xc4, 0x43, 0xf9, 0xff, 0x5f, 0x74,
0x2d, 0xb5, 0xe0, 0x1c, 0xab, 0xf4, 0x6e, 0xd5, 0xdb, 0xc8, 0x0c, 0xfb, 0x76, 0x3c, 0x38, 0x66,
0xf3, 0x7f, 0x01, 0x43, 0x7a, 0x30, 0x39, 0x02, 0x80, 0xa4, 0x11, 0xb3, 0x04, 0xd9, 0xe3, 0x57,
0x23, 0xf4, 0x07, 0xfc, 0x91, 0x8a, 0xc6, 0xcc, 0xa2, 0x16, 0x29, 0xb3, 0xe5, 0x76, 0x4a, 0xa8,
0x84, 0x19, 0xdc, 0xef, 0xfc, 0xb0, 0x63, 0x33, 0x0b, 0xfa, 0xf6, 0x68, 0x0b, 0x08, 0xea, 0x31,
0x52, 0xee, 0x99, 0xef, 0x43, 0x2a, 0xbe, 0x97, 0xad, 0xb3, 0xb9, 0x66, 0x7a, 0xae, 0xe1, 0x8f,
0x57, 0x86, 0xe5, 0xfe, 0x14, 0x3c, 0x81, 0xd0, 0x64, 0xf8, 0x86, 0x1a, 0x0b, 0x40, 0x58, 0xc9,
0x33, 0x49, 0xb8, 0x99, 0xc6, 0x2e, 0x94, 0x70, 0xee, 0x09, 0x88, 0xe1, 0x5c, 0x4e, 0x6c, 0x22,
0x72, 0xa7, 0x2a, 0x21, 0xdd, 0xd7, 0x1d, 0xfc, 0x63, 0x15, 0x0b, 0xde, 0x06, 0x9c, 0xf3, 0x28,
0xf3, 0xac, 0x4a, 0xa8, 0xb5, 0x50, 0xca, 0x9b, 0xcc, 0x0a, 0x04, 0xfe, 0x3f, 0x98, 0x68, 0x81,
0xac, 0x24, 0x53, 0xea, 0x1f, 0x1c, 0x6e, 0x5e, 0xca, 0xe8, 0x31, 0x0d, 0x08, 0x12, 0xf3, 0x26,
0xf8, 0x5e, 0xeb, 0x10, 0x27, 0xae, 0xaa, 0xc3, 0xad, 0x6c, 0xc1, 0x89, 0xdb, 0x7d, 0x5a, 0x12,
0x55, 0xad, 0x11, 0x19, 0xa1, 0xa9, 0x8f, 0x0b, 0x6d, 0x78, 0x8d, 0x1c, 0xdf, 0xe5, 0x63, 0x82,
0x0b, 0x7d, 0x23, 0x04, 0xb4, 0x75, 0x8c, 0xed, 0x77, 0xfc, 0x1a, 0x85, 0x29, 0x11, 0xe0, 0x61,
]);
其中,密钥算法的值取自枚举类HuksKeyAlg。
- RSA密钥对材料格式:
| 密钥算法 | 密钥大小 | 模数n长度Ln | 公钥指数e长度Le | 私钥指数d长度Ld | n | e | d |
|---|---|---|---|---|---|---|---|
| 4字节 | 4字节 | 4字节 | 4字节 | 4字节 | Ln字节 | Le字节 | Ld字节 |
- ECC密钥对材料格式:
| 密钥算法 | 密钥大小 | 坐标x长度Lx | 坐标y长度Ly | 坐标z长度Lz | x | y | z |
|---|---|---|---|---|---|---|---|
| 4字节 | 4字节 | 4字节 | 4字节 | 4字节 | Lx字节 | Ly字节 | Lz字节 |
- DSA密钥对材料格式:
| 密钥算法 | 密钥大小 | 私钥x长度Lx | 公钥y长度Ly | 素数p长度Lp | 素因子q长度Lq | g长度Lg | x | y | p | q | g |
|---|---|---|---|---|---|---|---|---|---|---|---|
| 4字节 | 4字节 | 4字节 | 4字节 | 4字节 | 4字节 | 4字节 | Lx字节 | Ly字节 | Lp字节 | Lq字节 | Lg字节 |
- DH密钥对材料格式:
| 密钥算法 | 密钥大小 | 公钥pk长度Lpk | 私钥sk长度Lsk | 保留字段 | pk | sk |
|---|---|---|---|---|---|---|
| 4字节 | 4字节 | 4字节 | 4字节 | 4字节 | Lpk字节 | Lsk字节 |
- Curve25519密钥对材料格式:
| 密钥算法 | 密钥大小 | 公钥pk长度Lpk | 私钥sk长度Lsk | 保留字段 | pk | sk |
|---|---|---|---|---|---|---|
| 4字节 | 4字节 | 4字节 | 4字节 | 4字节 | Lpk字节 | Lsk字节 |
公钥材料
在公钥导出/导入时,密钥材料采用标准的X.509规范的DER格式封装。
如下是一个DER编码的ECC公钥:
let eccP256PubKey = new Uint8Array([
0x30, 0x59, 0x30, 0x13, 0x06, 0x07, 0x2a, 0x86, 0x48, 0xce, 0x3d, 0x02, 0x01, 0x06, 0x08, 0x2a,
0x86, 0x48, 0xce, 0x3d, 0x03, 0x01, 0x07, 0x03, 0x42, 0x00, 0x04, 0xc0, 0xfe, 0x1c, 0x67, 0xde,
0x86, 0x0e, 0xfb, 0xaf, 0xb5, 0x85, 0x52, 0xb4, 0x0e, 0x1f, 0x6c, 0x6c, 0xaa, 0xc5, 0xd9, 0xd2,
0x4d, 0xb0, 0x8a, 0x72, 0x24, 0xa1, 0x99, 0xaf, 0xfc, 0x3e, 0x55, 0x5a, 0xac, 0x99, 0x3d, 0xe8,
0x34, 0x72, 0xb9, 0x47, 0x9c, 0xa6, 0xd8, 0xfb, 0x00, 0xa0, 0x1f, 0x9f, 0x7a, 0x41, 0xe5, 0x44,
0x3e, 0xb2, 0x76, 0x08, 0xa2, 0xbd, 0xe9, 0x41, 0xd5, 0x2b, 0x9e]);
私钥材料
复用密钥对的材料格式,私钥材料的封装是把密钥对材料Header中的公钥部分的长度字段置0,同时密钥对材料原文部分拼接私钥材料即可。
私钥材料 = 密钥对材料Header + 私钥材料原文
以RSA私钥材料为例:
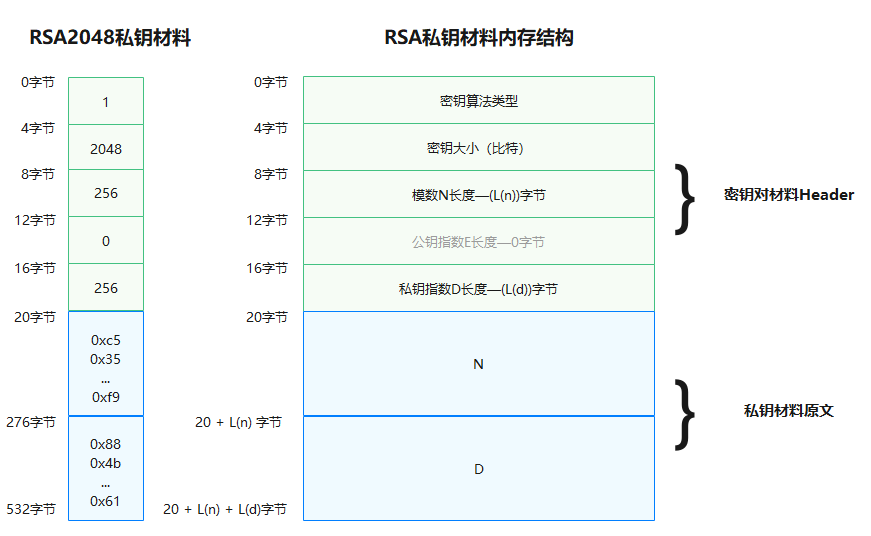
let rsa2048PrivateKeyMaterial = new Uint8Array([
0x01, 0x00, 0x00, 0x00, // 密钥算法:huks.HuksKeyAlg.HUKS_ALG_RSA = 1
0x00, 0x08, 0x00, 0x00, // 密钥大小(比特):2048
0x00, 0x01, 0x00, 0x00, // 模数n长度(字节):256
0x00, 0x00, 0x00, 0x00, // 公钥指数e长度(字节):0
0x00, 0x01, 0x00, 0x00, // 私钥指数d长度(字节):256
// 模数n
0xc5, 0x35, 0x62, 0x48, 0xc4, 0x92, 0x87, 0x73, 0x0d, 0x42, 0x96, 0xfc, 0x7b, 0x11, 0x05, 0x06,
0x0f, 0x8d, 0x66, 0xc1, 0x0e, 0xad, 0x37, 0x44, 0x92, 0x95, 0x2f, 0x6a, 0x55, 0xba, 0xec, 0x1d,
0x54, 0x62, 0x0a, 0x4b, 0xd3, 0xc7, 0x05, 0xe4, 0x07, 0x40, 0xd9, 0xb7, 0xc2, 0x12, 0xcb, 0x9a,
0x90, 0xad, 0xe3, 0x24, 0xe8, 0x5e, 0xa6, 0xf8, 0xd0, 0x6e, 0xbc, 0xd1, 0x69, 0x7f, 0x6b, 0xe4,
0x2b, 0x4e, 0x1a, 0x65, 0xbb, 0x73, 0x88, 0x6b, 0x7c, 0xaf, 0x7e, 0xd0, 0x47, 0x26, 0xeb, 0xa5,
0xbe, 0xd6, 0xe8, 0xee, 0x9c, 0xa5, 0x66, 0xa5, 0xc9, 0xd3, 0x25, 0x13, 0xc4, 0x0e, 0x6c, 0xab,
0x50, 0xb6, 0x50, 0xc9, 0xce, 0x8f, 0x0a, 0x0b, 0xc6, 0x28, 0x69, 0xe9, 0x83, 0x69, 0xde, 0x42,
0x56, 0x79, 0x7f, 0xde, 0x86, 0x24, 0xca, 0xfc, 0xaa, 0xc0, 0xf3, 0xf3, 0x7f, 0x92, 0x8e, 0x8a,
0x12, 0x52, 0xfe, 0x50, 0xb1, 0x5e, 0x8c, 0x01, 0xce, 0xfc, 0x7e, 0xf2, 0x4f, 0x5f, 0x03, 0xfe,
0xa7, 0xcd, 0xa1, 0xfc, 0x94, 0x52, 0x00, 0x8b, 0x9b, 0x7f, 0x09, 0xab, 0xa8, 0xa4, 0xf5, 0xb4,
0xa5, 0xaa, 0xfc, 0x72, 0xeb, 0x17, 0x40, 0xa9, 0xee, 0xbe, 0x8f, 0xc2, 0xd1, 0x80, 0xc2, 0x0d,
0x44, 0xa9, 0x59, 0x44, 0x59, 0x81, 0x3b, 0x5d, 0x4a, 0xde, 0xfb, 0xae, 0x24, 0xfc, 0xa3, 0xd9,
0xbc, 0x57, 0x55, 0xc2, 0x26, 0xbc, 0x19, 0xa7, 0x9a, 0xc5, 0x59, 0xa3, 0xee, 0x5a, 0xef, 0x41,
0x80, 0x7d, 0xf8, 0x5e, 0xc1, 0x1d, 0x32, 0x38, 0x41, 0x5b, 0xb6, 0x92, 0xb8, 0xb7, 0x03, 0x0d,
0x3e, 0x59, 0x0f, 0x1c, 0xb3, 0xe1, 0x2a, 0x95, 0x1a, 0x3b, 0x50, 0x4f, 0xc4, 0x1d, 0xcf, 0x73,
0x7c, 0x14, 0xca, 0xe3, 0x0b, 0xa7, 0xc7, 0x1a, 0x41, 0x4a, 0xee, 0xbe, 0x1f, 0x43, 0xdd, 0xf9,
// 私钥指数d
0x88, 0x4b, 0x82, 0xe7, 0xe3, 0xe3, 0x99, 0x75, 0x6c, 0x9e, 0xaf, 0x17, 0x44, 0x3e, 0xd9, 0x07,
0xfd, 0x4b, 0xae, 0xce, 0x92, 0xc4, 0x28, 0x44, 0x5e, 0x42, 0x79, 0x08, 0xb6, 0xc3, 0x7f, 0x58,
0x2d, 0xef, 0xac, 0x4a, 0x07, 0xcd, 0xaf, 0x46, 0x8f, 0xb4, 0xc4, 0x43, 0xf9, 0xff, 0x5f, 0x74,
0x2d, 0xb5, 0xe0, 0x1c, 0xab, 0xf4, 0x6e, 0xd5, 0xdb, 0xc8, 0x0c, 0xfb, 0x76, 0x3c, 0x38, 0x66,
0xf3, 0x7f, 0x01, 0x43, 0x7a, 0x30, 0x39, 0x02, 0x80, 0xa4, 0x11, 0xb3, 0x04, 0xd9, 0xe3, 0x57,
0x23, 0xf4, 0x07, 0xfc, 0x91, 0x8a, 0xc6, 0xcc, 0xa2, 0x16, 0x29, 0xb3, 0xe5, 0x76, 0x4a, 0xa8,
0x84, 0x19, 0xdc, 0xef, 0xfc, 0xb0, 0x63, 0x33, 0x0b, 0xfa, 0xf6, 0x68, 0x0b, 0x08, 0xea, 0x31,
0x52, 0xee, 0x99, 0xef, 0x43, 0x2a, 0xbe, 0x97, 0xad, 0xb3, 0xb9, 0x66, 0x7a, 0xae, 0xe1, 0x8f,
0x57, 0x86, 0xe5, 0xfe, 0x14, 0x3c, 0x81, 0xd0, 0x64, 0xf8, 0x86, 0x1a, 0x0b, 0x40, 0x58, 0xc9,
0x33, 0x49, 0xb8, 0x99, 0xc6, 0x2e, 0x94, 0x70, 0xee, 0x09, 0x88, 0xe1, 0x5c, 0x4e, 0x6c, 0x22,
0x72, 0xa7, 0x2a, 0x21, 0xdd, 0xd7, 0x1d, 0xfc, 0x63, 0x15, 0x0b, 0xde, 0x06, 0x9c, 0xf3, 0x28,
0xf3, 0xac, 0x4a, 0xa8, 0xb5, 0x50, 0xca, 0x9b, 0xcc, 0x0a, 0x04, 0xfe, 0x3f, 0x98, 0x68, 0x81,
0xac, 0x24, 0x53, 0xea, 0x1f, 0x1c, 0x6e, 0x5e, 0xca, 0xe8, 0x31, 0x0d, 0x08, 0x12, 0xf3, 0x26,
0xf8, 0x5e, 0xeb, 0x10, 0x27, 0xae, 0xaa, 0xc3, 0xad, 0x6c, 0xc1, 0x89, 0xdb, 0x7d, 0x5a, 0x12,
0x55, 0xad, 0x11, 0x19, 0xa1, 0xa9, 0x8f, 0x0b, 0x6d, 0x78, 0x8d, 0x1c, 0xdf, 0xe5, 0x63, 0x82,
0x0b, 0x7d, 0x23, 0x04, 0xb4, 0x75, 0x8c, 0xed, 0x77, 0xfc, 0x1a, 0x85, 0x29, 0x11, 0xe0, 0x61,
]);